Why Google Is Suddenly Blocking Some Android Users From Sideloading Apps

Google says it's working with the Cyber Security Agency of Singapore (CSA) to roll the new security feature out in the coming weeks. When it's live, users downloading APK files from third-party sources may find some of them won't work. Google is targeting a collection of permissions that are commonly used in malware, particularly financial fraud. Here are the risky permissions.
- RECEIVE_SMS: Malware uses this permission to intercept two-factor codes to access the victim's accounts.
- READ_SMS: Used to read the two-factor codes in received SMS messages.
- BIND_Notifications: Can read or dismiss notifications, potentially hiding the malware's activity from the user.
- Accessibility: A service usually aimed at helping people with disabilities use their devices, Accessibility can also allow malware to emulate taps and monitor user activities.
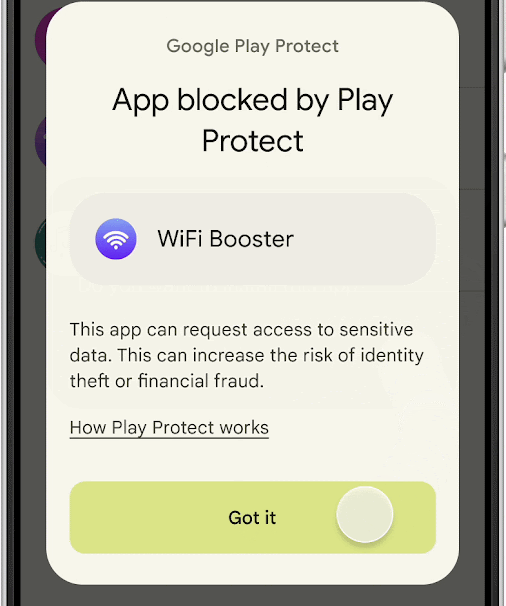
According to Google, a downloaded APK file that declares any of those dangerous permissions won't be installed. Users will get an explanation of the block, but there won't be an option to bypass, which might annoy people who've gotten used to installing any ill-advised app they might come across. There will be no change for apps installed from the Google Play Store, and the installation blocks will only be deployed on Google-certified Android devices with Play Services.
Google says it will work with the CSA to monitor the results of the pilot program. Google didn't mention any plans to expand the test, but that could come after the Android maker better understands the impact of blocking these sideloaded apps. In the meantime, it advises developers to make sure their apps only declare the permissions they absolutely need.

