OpenDNS and Kaspersky Take On Conficker
Internet security and infrastructure service provider, OpenDNS, and security software provider, Kaspersky Lab, have collaborated to help alert users that their systems are infected by one of the "most widely-spread" worms to come our way, the Conficker worm. The Conficker worm, which is also called Kido and Downadup, first popped up "in late 2008," and according to some reports has already infected "as many as 15 million computers around the world."
Conficker infects systems by taking advantage of a known vulnerability in the Windows' Server service in Windows 2000, Windows XP, Windows Server 2003, Windows Vista, and Windows Server 2008. (While a fix for this vulnerability has been available from Microsoft since October 23, 2008, not all users have necessarily installed the fix or run the relevant Windows Updates to ensure that their systems are properly protected.) Once a system is infected, Conficker uses brute-force, dictionary attacks of Administrator passwords on networks that the infected system is connected to; if Conficker successfully guesses an Administrator password, it can spread itself onto shared folders on the network. Conficker also places special DLLs and an autorun.inf file into shared folders and removable drives, such as USB flash drives; whenever a user attaches to an infected drive or shared folder, the Conficker autorun routine can automatically infect the system. (As the United States Computer Emergency Readiness Team warned a few weeks ago, just disabling Windows' AutoRun is not enough to avoid potential infection by the Conficker worm.) Once Conficker has infected a system, it then attempts to go online to receive additional instructions for next steps:
"Conficker, also known as Downadup, uses a set of seemingly random domain names as a meeting place for the virus to exchange data with its author, such as how many new machines each host has brought into the botnet, or details on any code upgrades or attacks the owner wants to take place. These domain names are generated using an algorithm so they change every day, making traditional methods like revoking domain registrations used by botnet authors ineffective."
 This is where OpenDNS and Kaspersky Lab enter the picture. Kaspersky has been able to "preemptively predict the domains that will be used in coming days by the virus," and Kaspersky is sharing this information with OpenDNS. Any user or organization that uses OpenDNS's alternative DNS service for their systems, automatically takes advantage of OpenDNS's "Botnet Protection," which will prevent a system from connecting to any of these predicted domains. This obviously doesn't prevent a system from getting infected by Conficker in the first place, but it will prevent Conficker from receiving any "further actions at the instruction of the virus author." Additionally, network administrators will receive an e-mail alert letting them know that a system attempted to connect to one of these predicted domains. This alerts the administrator that the Conficker worm has infected at least one system on the network, and "this insight then gives network administrators the knowledge necessary to disable the worm and prevent it from causing damage."
This is where OpenDNS and Kaspersky Lab enter the picture. Kaspersky has been able to "preemptively predict the domains that will be used in coming days by the virus," and Kaspersky is sharing this information with OpenDNS. Any user or organization that uses OpenDNS's alternative DNS service for their systems, automatically takes advantage of OpenDNS's "Botnet Protection," which will prevent a system from connecting to any of these predicted domains. This obviously doesn't prevent a system from getting infected by Conficker in the first place, but it will prevent Conficker from receiving any "further actions at the instruction of the virus author." Additionally, network administrators will receive an e-mail alert letting them know that a system attempted to connect to one of these predicted domains. This alerts the administrator that the Conficker worm has infected at least one system on the network, and "this insight then gives network administrators the knowledge necessary to disable the worm and prevent it from causing damage."
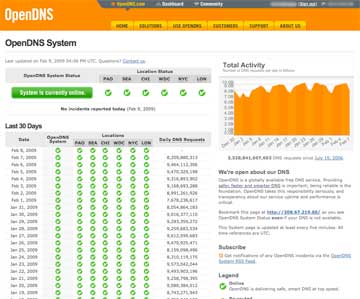
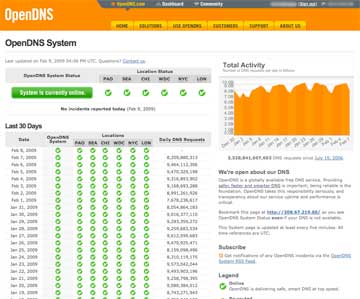
OpenDNS is free service that can be set up on individual systems, routers, or even DNS routers; it serves between 8 and 9 billion DNS requests per day. OpenDNS generates revenue by displaying ads on a redirected OpenDNS page when a user tries to access a nonexistent webpage.
Conficker infects systems by taking advantage of a known vulnerability in the Windows' Server service in Windows 2000, Windows XP, Windows Server 2003, Windows Vista, and Windows Server 2008. (While a fix for this vulnerability has been available from Microsoft since October 23, 2008, not all users have necessarily installed the fix or run the relevant Windows Updates to ensure that their systems are properly protected.) Once a system is infected, Conficker uses brute-force, dictionary attacks of Administrator passwords on networks that the infected system is connected to; if Conficker successfully guesses an Administrator password, it can spread itself onto shared folders on the network. Conficker also places special DLLs and an autorun.inf file into shared folders and removable drives, such as USB flash drives; whenever a user attaches to an infected drive or shared folder, the Conficker autorun routine can automatically infect the system. (As the United States Computer Emergency Readiness Team warned a few weeks ago, just disabling Windows' AutoRun is not enough to avoid potential infection by the Conficker worm.) Once Conficker has infected a system, it then attempts to go online to receive additional instructions for next steps:
"Conficker, also known as Downadup, uses a set of seemingly random domain names as a meeting place for the virus to exchange data with its author, such as how many new machines each host has brought into the botnet, or details on any code upgrades or attacks the owner wants to take place. These domain names are generated using an algorithm so they change every day, making traditional methods like revoking domain registrations used by botnet authors ineffective."
 This is where OpenDNS and Kaspersky Lab enter the picture. Kaspersky has been able to "preemptively predict the domains that will be used in coming days by the virus," and Kaspersky is sharing this information with OpenDNS. Any user or organization that uses OpenDNS's alternative DNS service for their systems, automatically takes advantage of OpenDNS's "Botnet Protection," which will prevent a system from connecting to any of these predicted domains. This obviously doesn't prevent a system from getting infected by Conficker in the first place, but it will prevent Conficker from receiving any "further actions at the instruction of the virus author." Additionally, network administrators will receive an e-mail alert letting them know that a system attempted to connect to one of these predicted domains. This alerts the administrator that the Conficker worm has infected at least one system on the network, and "this insight then gives network administrators the knowledge necessary to disable the worm and prevent it from causing damage."
This is where OpenDNS and Kaspersky Lab enter the picture. Kaspersky has been able to "preemptively predict the domains that will be used in coming days by the virus," and Kaspersky is sharing this information with OpenDNS. Any user or organization that uses OpenDNS's alternative DNS service for their systems, automatically takes advantage of OpenDNS's "Botnet Protection," which will prevent a system from connecting to any of these predicted domains. This obviously doesn't prevent a system from getting infected by Conficker in the first place, but it will prevent Conficker from receiving any "further actions at the instruction of the virus author." Additionally, network administrators will receive an e-mail alert letting them know that a system attempted to connect to one of these predicted domains. This alerts the administrator that the Conficker worm has infected at least one system on the network, and "this insight then gives network administrators the knowledge necessary to disable the worm and prevent it from causing damage."OpenDNS is free service that can be set up on individual systems, routers, or even DNS routers; it serves between 8 and 9 billion DNS requests per day. OpenDNS generates revenue by displaying ads on a redirected OpenDNS page when a user tries to access a nonexistent webpage.

