Data breaches are becoming increasingly common and more sophisticated, putting consumers' personal information and financials at risk. Not only can these data breaches lead to identity theft, but some can even lead to money being siphoned out of bank accounts and illegal purchases made on credit cards. The responsibility for preventing these breaches falls on many shoulders, including merchants, consumers, and even Internet service providers (ISPs). Once such ISP, Verizon, recently analyzed "
four years of data from over 500 cases worked by the Verizon Business Investigative Response team," to produce a report that gives an in-depth look into how data breaches are occurring in four major industry groups: financial services, food and beverage, retail, and technology services.
|
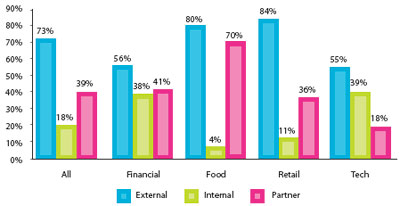
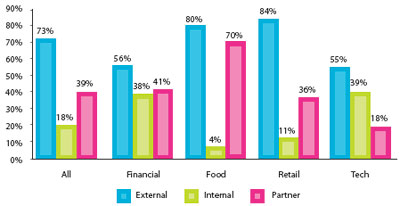
Sources of data breaches (Credit: Verizon)
|
As expected, the majority of data breaches come from external sources, such as from hacking and coding errors, for all four sectors. The second most-often sited source of data breaches for three out of four of the industry sectors is from partners--"
partners include any third party sharing a business relationship with the organization," such as "
vendors, suppliers, [and]
contractors." The food industry is especially susceptible to data breaches from its partners, with partner-originated data breaches at close to the same level as data breaches from external sources. The least likely source of data breaches for three out of four of the industry sectors is from internal sources, such as "
company executives, employees, and interns--as well as other assets such as physical facilities and information systems." The one deviation from the norm here, however, is the technology services sector, which sees more data breaches from internal sources than from partners. The Verizon report theorizes on the anomaly this way:
 |
| Internal sources (Credit: Verizon) |
 |
Threat categories (click to enlarge)
(Credit: Verizon)
|
"Tech services are often in the role of 'the partner' to the other
industries, providing management, hosting, and other services. It
stands to reason that organizations in the industry likely employ a
high percentage of tech-savvy staff and grant them high levels of
access to numerous systems. Unfortunately, some find that access to
sensitive and valuable resources us a temptation too hard to resist."As to the types of threats that the industries face, hacking is less of
an actual threat for the financial and tech sectors than for food and
retail. This is likely a result of the more sophisticated security
measures in place for the financial and tech sectors. Threats resulting
from errors, however, were high for all four industries. The
predominant source of errors for all four industries is from omissions,
such as "
standard security measures that were believed to have been implemented, but in actuality were not."
The financial sector had the lowest incident of omission-related
errors, while the technology services sector had the highest. Although
much less pronounced than omissions, errors from misconfiguration were
the second most-likely source of errors for all four industries.
Threats from deceit were sited as a significant source for the financial
industry, while misuse was a major threat source for the technical
services sector.
 |
Data types (click to enlarge)
(Credit: Verizon)
|
The Verizon Business report breaks down data breach attack difficulty into four levels: None (capable by the "
average user"); Low ("
low-level skills"); Moderate ("
skilled techniques"); and High ("
advanced skills").
For the food and retail industries, the majority of the attacks were
low-difficulty-level attacks. The financial and technology services
sectors saw more moderate-difficulty-level attacks. The tech industry
saw the greatest level of high-difficulty-level attacks of the four
industries.
Credit card data is consistently the most frequent type of data
that is breached for all industry sectors; but it is especially
egregious in the food and retail industries. For all sectors, except
for food, the second-most breached data type is personal information.
Authentication data is also a prominent breached data type for the
financial and technology sectors, compared to the other industries.
Sadly, the overwhelming majority of data breaches for all sectors are discovered by third parties; breach detection via internal event monitoring and log analysis are low for all industries, including financial and tech. The report indicates that this "
suggests that breach detection is an almost completely reactive process... It would be nice to see a little more proactive approach." The time it takes to discover data breaches can sometimes go on for months, or even years in the case of the retail industry.
 |
Discovery time span (click to enlarge)
(Credit: Verizon)
|
"There is a striking difference between industries in the length of
time that passes before an incident is discovered. While we expected
longer intervals in Food and Beverage, we were shocked to find that 90
percent of breaches go undiscovered for months. Retail and Tech
Services post better times but not by much. Even though Financial
Services firms become aware of breaches within days in 50 percent of
the cases, a sizeable number still go undetected for weeks and months.
While this seems like an impressive feat relative to other groups, no
industry can claim victory in the contest of timely breach discovery."The takeaway from all this is going to be different depending on the specific industry. It would appear that the retail and food industries have the greatest amount of work ahead of them in order to attempt to minimize data breaches. But the tech and financial sectors aren't off the hook either--they still have plenty to do as well. Perhaps most disconcerting is how all of these industries appear to lack effective proactive means to discover and prevent data breaches. Perhaps crime does pay?